How Legitimate IT Tools Are Being Weaponised Against Businesses
In a stark reminder that threat actors continue to favour stealth over sophistication, security researchers have uncovered a series of incidents where legitimate employee‑monitoring and remote‑support tools were hijacked to deploy ransomware. Instead of relying on custom malware, attackers are increasingly abusing trusted IT software already allowed inside corporate networks — making detection dramatically harder.
🧩 What Huntress Discovered
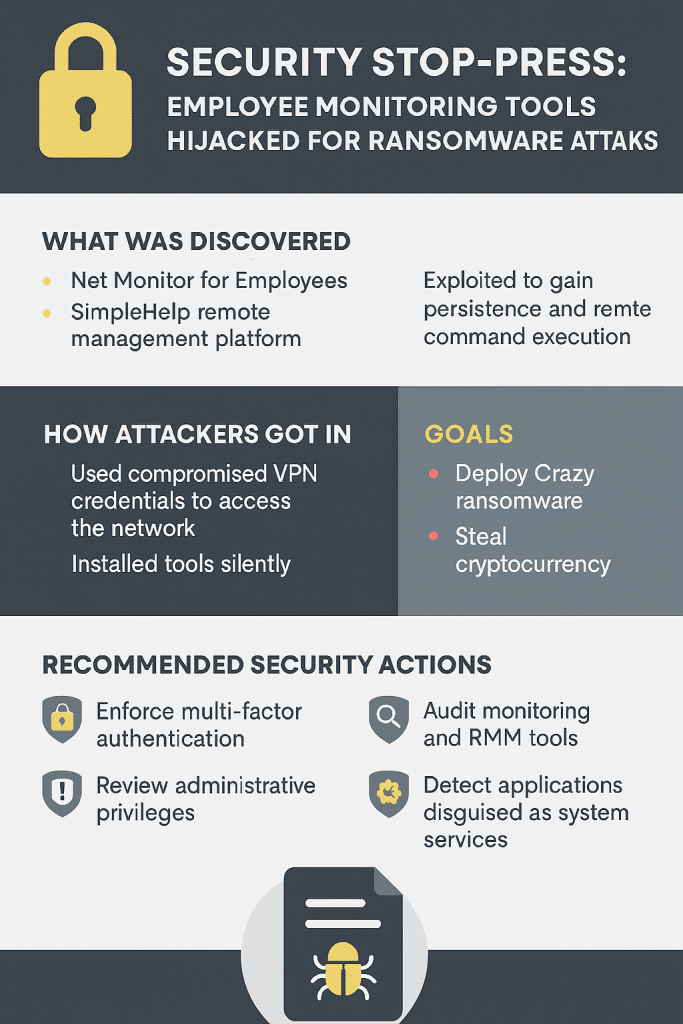
Security firm Huntress observed two separate intrusions in January and February 2026 where attackers chained together:
- Net Monitor for Employees Professional
- SimpleHelp remote management platform
These commercial tools were used to achieve:
- Persistent remote access
- Hands‑on‑keyboard reconnaissance
- Command execution
- File transfer
- Attempted ransomware deployment
Net Monitor for Employees includes a powerful pseudo‑terminal (winpty-agent.exe) capable of full command execution, enabling hackers to perform manual reconnaissance and manipulation across systems.
SimpleHelp acted as a redundant persistence channel, thanks to its lightweight agent and ability to masquerade as legitimate Windows services.
🎯 How the Attackers Gained Access
In at least one case, the intrusion began with:
- Compromised vendor SSL VPN credentials
From there, threat actors:
- Connected to internal systems via RDP
- Installed Net Monitor using silent msiexec execution
- Deployed a disguised SimpleHelp client, sometimes mimicking OneDrive or Visual Studio host executables
This “living‑off‑the‑land” approach allowed them to blend in with normal administrative traffic.
💣 Attempted Ransomware Deployment
In both investigations, attackers attempted to deploy Crazy ransomware, a variant associated with the VoidCrypt family.
They dropped multiple copies of the ransomware binary (e.g., encrypt.exe) — often repeatedly due to failed execution attempts.
Huntress confirmed shared infrastructure, overlapping filenames, and consistent tradecraft, strongly indicating a single threat actor or group behind both incidents.
🏦 Cryptocurrency Theft Indicators
Attackers configured SimpleHelp to monitor cryptocurrency‑related keywords, indicating secondary financial motives such as:
- Wallet monitoring
- Exchange tracking
- Potential credential theft
Keywords included Metamask, Exodus, Binance, KuCoin, and more.
This shows the operation wasn’t just about ransomware — it appears financially opportunistic in multiple ways.
🛡️ Why These Attacks Matter
These intrusions relied on:
- Stolen credentials
- Misuse of legitimate tools
- Service masquerading
- Disabled Windows Defender attempts
They did NOT rely on zero‑days or novel malware — making them much more likely to slip past conventional antivirus solutions.
This highlights a growing trend:
Attackers increasingly prefer turning trusted IT tools into remote‑access trojans rather than obtaining or building custom malware.
🔐 What Businesses Should Do Immediately
1. Enforce Multi‑Factor Authentication Everywhere
Compromised VPN and RDP credentials were key in these attacks.
2. Audit All Remote Monitoring & Admin Tools
Review:
- RMM software
- Employee monitoring tools
- Remote‑support clients
Ensure each deployment is approved, documented and monitored.
3. Restrict Administrative Privileges
Minimise who can install or run remote‑access agents.
4. Watch for Silent or Unusual msiexec Installations
Attackers installed Net Monitor silently to avoid detection.
5. Monitor for Process & Service Masquerading
SimpleHelp and Net Monitor were disguised as legitimate Windows components.
6. Detect Attempts to Disable Security Controls
The attackers tried to shut down Windows Defender services.
🌐 AEO (Answer Engine Optimisation) Summary
Q: What happened?
Attackers abused legitimate tools (Net Monitor for Employees & SimpleHelp) to gain persistence and attempt Crazy ransomware deployment.
[huntress.com]
Q: How did they get in?
Through compromised VPN credentials and silent tool installations.
[gbhackers.com]
Q: What were the attackers’ goals?
Ransomware deployment + cryptocurrency monitoring/credential theft.
[bleepingcomputer.com]
Q: What should businesses do?
Enforce MFA, audit RMM tools, limit admin rights, monitor for disguised services and unusual installs.
[socprime.com]
🔚 Final Thoughts
This new wave of attacks reinforces a critical message:
Your biggest cybersecurity risk isn’t always malware — it’s the misuse of the tools you already trust.
By tightening remote‑access controls, enforcing MFA, and actively auditing any employee‑monitoring or RMM tools, organisations can drastically reduce their exposure to these stealthy, high‑impact threats.
Ready to Protect Your Business?
Contact EC Computers today for a Procurement Review and discover how we can help you stay secure.
📞 Call us: 0117 200 1000
📧 Email: Contact-us form
Further reading: Managed IT Services and Support – Privacy compliance and new 2025 laws